
What does it mean when a busy Bitcoin exchange suddenly stops all activity? Next, their website mysteriously goes offline. Then, their entire Twitter feed suddenly disappears.
Something very big and very bad is going down.
In February 2014, this very scenario played out with the Japan-based Mt. Gox cryptocurrency exchange.
The company had been hacked, and the results were devastating.
Before anyone even knew exactly what had happened, leaders of other Bitcoin companies were scrambling to reassure investors and keep up confidence in Bitcoin.
So, what happened in the Mt. Gox hack? Let’s find out.
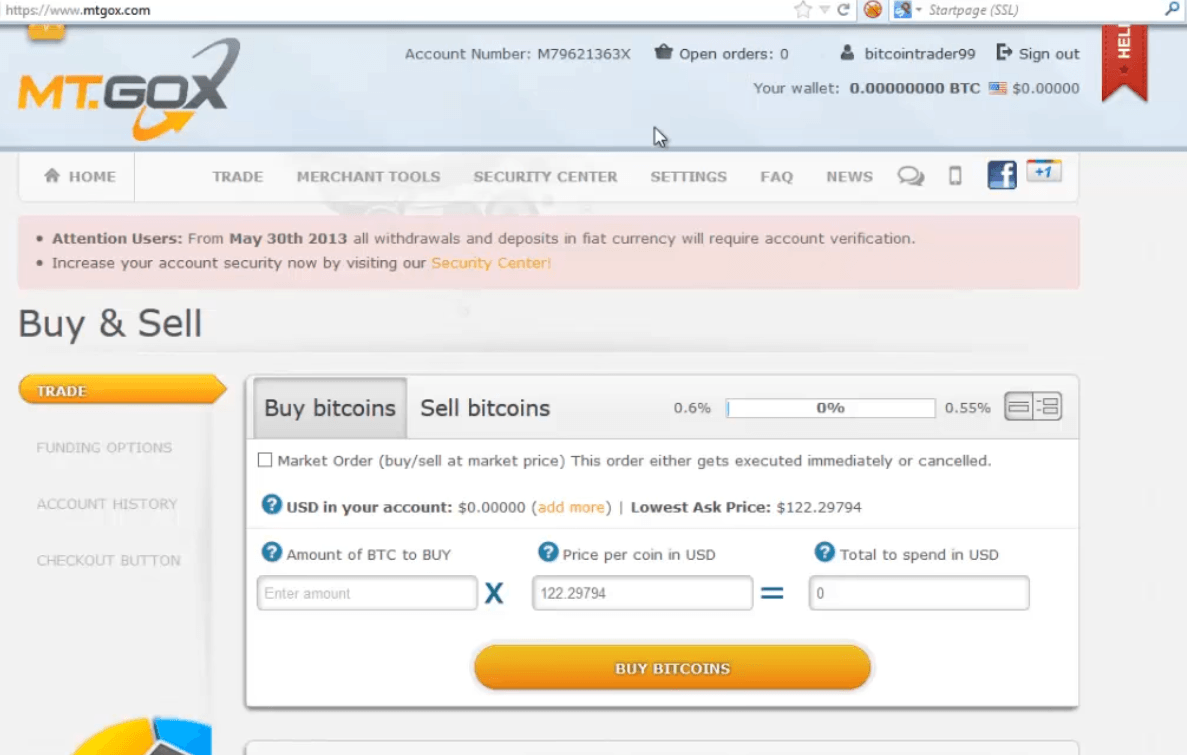
The company was started by US programmer Jed McCaleb in 2010 and sold to French developer Mark Karpelés in 2011.

Mt. Gox was more than a big player in the cryptocurrency world. At its peak in 2013, the exchange handled a whopping 70% of all bitcoin transactions worldwide.
This dipped a little to 70% by the beginning of 2014, but the company was still going strong.
Until…
Mt. Gox took a devastating hit in the largest Bitcoin hack to date. Hackers accessed and stole 740,000 bitcoin from Mt. Gox customers and 100,000 from the company itself, roughly the equivalent of $460 million at the time.
The event quickly spiraled out of control and the company was bankrupt by the end of February 2014.

Though everything exploded in February 2014, it’s now suspected that hacking activity was going on as early as 2011.
In June of 2011, the company experienced its first hack in which hackers got hold of Mt. Gox auditor’s computer and changed the price of bitcoin to 1 cent.
Then they started buying bitcoin at this artificial price using the private hot wallet keys of Mt. Gox customers, obtaining about 2,000 bitcoin.
On top of that:
Customers bought about 650 bitcoin, of which 0 BTC was ever returned.
After this, Mt. Gox tightened security, but it wasn’t enough to protect the exchange.
Investigations of the 2014 fiasco reveal that the Mt. Gox private key was unencrypted and stolen back in 2011. It’s unclear whether this information was obtained through a hack or with the help of an insider.

From there, the culprits began skimming bitcoins from customer accounts over the next couple of years.
The Mt. Gox system appears to have interpreted the thefts as transfers to more secure addresses, leaving the company oblivious to the drain.
➤ MORE: 2016 Bitfinex hack: 119,756 bitcoin stolen
Amazingly enough, although the company appears to be in the dark, they were technically insolvent for nearly two years before the hack became public.
By mid-2013, a year in which the company seemed to be enjoying huge success, they had already lost nearly all of their bitcoin.
It’s even possible about 80,000 was already missing when Mark Karpelés bought the exchange in 2011.
How did nobody know what was going on?
Many former employees cite mismanagement and disorganization within the company.
An anonymous developer revealed that the company didn’t even use version control software. This industry-standard tool was used to prevent colleagues from accidentally overwriting another’s work if they happened to be working on the same file.
Another problem was that the only person who could approve changes to the site’s source code was Mark Karpelés. This meant that even important security updates and bug fixes might wait weeks for approval.
Other, more public problems were already beginning to surface in 2013.
In May of that year, Coinlab, a former business partner sued Mt. Gox for $75 million, claiming breach of contract. They were supposed to take over Mt. Gox’s American clientele, but due to Mt. Gox breaching their contract, this never came about.
On top of that, Mt. Gox was under investigation by the US Department of Homeland due to claims that a Mt. Gox subsidiary was operating without a license in the U.S. Eventually the U.S. government seized over $5 million from Mt. Gox.
Shortly after the hack in 2014, Mt. Gox reportedly found 200,000 bitcoins in old-format digital wallets the company had been using before June 2011. They promised to disburse these bitcoins to victims of the hack.

However:
The bitcoins have been held in trust for the creditors for the last few years since the company is under bankruptcy protection.
A judge also dismissed a Canadian class action lawsuit against Mt Gox.
➤ MORE: Bitcoin Treasuries: List of companies that own BTC
A Japanese court finally put a halt to the bankruptcy state, which would have turned assets over to Mt. Gox’s owners and instead put it under civil rehabilitation law. Under this law, as much of the company’s assets as possible will be turned over to Mt. Gox’s creditors when all is said and done.
Since then, promised deadlines for the disbursement of the bitcoins have come and gone.
Additionally, Russian lawyer Alexander Zheleznikov, managing partner of ZP Legal, has approached Mt. Gox saying he believes he can help recover up to 200,000 of the lost bitcoin. He believes the bitcoin ended up in another now-defunct exchange, the Russian/European BTC-e. The plan involves recovering the bitcoins from Russian nationals through legal action.
Of course, ZP legal is more than happy to help but may charge up to a 75% tax of the recovered value for their efforts.
On the plus side, they’ve promised to only accept payment if they are successful in recuperating bitcoins.
In January 2021, CoinLab Inc. (who was responsible for handling North American transactions for Mt. Gox) settled with Nobuaki Kobayashi, the trustee of the Mt. Gox bankruptcy.
In October of 2021, the funds held by a Japanese trustee for Mt Gox say that creditors have come to an approved plan to distribute the 141,686 Bitcoins (valued at more than $9 billion based on the record high price of more than $66,000 at the time). As of yet, a payout date has not been determined.
In that settlement, creditors could forgo continuing to trial in exchange for as much as 90% of the existing Bitcoin tied up in bankruptcy.
Of course, Coinlab is only one creditor.
Others are suing Mt. Gox as well. Not to mention the users whose Bitcoins were stolen from the platform, and who are in litigation to recover some of their stolen funds.
Unfortunately, there is only about .23 BTC in custody for every Bitcoin owed to users and creditors.
There are two different sets of Mt. Gox Bitcoins.
First, there are the coins that were stolen and no longer controlled by Mt. Gox or its trustees.
ZP Legal (mentioned above) believes they know who stole the coins in the first place - Russian nationals. ZP legal believes Alexander Vinnik and his exchange BTC-e (which was also shuttered in 2017 due to fraud) were laundering the stolen Bitcoins from the Mt. Gox hack and know who the hackers are. Vinnik was arrested in 2017 in Greece and was sentenced to 5 years in Prison for his role in BTC-e’s fraud scheme. ZP is trying to get Vinnik to cut a deal with authorities to turn over information about his alleged hacker clients responsible for the Mt. Gox hack.

Second, there are the coins that Mt. Gox never lost and are now being litigated over to decide who gets them as recompense.
These coins are being held by the Mt. Gox trustee Nobuaki Kobayashi until litigation is complete and a compensation order is established by the lawyers and the courts to settle the matter.
In June of 2021, it was announced that claimants would have until October to vote on Kobayashi’s proposal to them.
Kobayashi’s letter to claimants stated,
“We are pleased to inform you that the online voting function has been released on the online rehabilitation claim filing system — In addition to voting online for or against the Draft Rehabilitation Plan, it is anticipated that the System will be used by creditors for procedure for receiving repayments in the future.”
The main lesson learned from the Mt. Gox fiasco is that cryptocurrency, Bitcoin, and altcoins are a whole new ballpark, far different from the currently known financial world. Bankruptcy law was not adequate for dealing with the fallout and the shift to civil rehabilitation is an important precedent for the crypto community.
Six years have ticked by and people are still waiting for access to their frozen assets. This is unacceptable and serves as a warning to the cryptocurrency community to put better structures in place for when disaster strikes.
Of course, the ultimate goal is to prevent those disasters altogether, but hackers get more creative every year.
BuyBitcoinWorldWide writers are subject-matter experts and base their articles on firsthand information, like interviews with experts, white papers or original studies and experience. We also use trusted research and studies from other well-known sources. You can learn more about our editorial guidelines.